
The News: The Ransom Disclosure Act, a bill introduced last week by Senator Elizabeth Warren and U.S. House Representative Deborah Ross, would require the victims of ransomware attacks to report payments to their hackers within 48 hours. Read the proposed bill in its entirety here.
The Ransom Disclosure Act Proposed — Gives 48 Hours to Report Ransom Payments
Analyst Take: The proposed Ransom Disclosure Act is intended to provide an assist to the Department of Homeland Security, providing rapid data about ransomware payments, which will allow the government to quickly learn more about how hackers operate, how much money is involved in ransomware payments, and a better understanding of the extent of the ransomware threat. This makes a lot of sense, as the ability for the government to drive a more effective threat response is contingent upon the very sort of data the proposed bill would require.
The proposed bill would require companies, nonprofits, and local governments that acquiesce to ransomware demands to report those payments to the government within 48 hours of the payment. They would need to specifically report the date the ransom was demanded and the amount demanded, along with the date and amount ultimately paid. The affected entities would also need to report what currency was used to pay off the ransom demand. This signals the rise in popularity of cryptocurrency payment demands by ransomware gangs.
The good news on that front, however, is that recent ransomware instances, the largest of which is possibly the Colonial Pipeline hack, have shown us that cryptocurrency ransomware payments are increasingly trackable and recoverable.
Why is Ransom Payment Reporting Important?
Ransom payment reporting — why is this important? Ransomware has seen a significant uptick so far in 2021, with global attack volume increasing by 151 percent for the first six months of the year as compared with the year-ago half, and attacks happening about every 11 seconds. Meanwhile, the FBI has warned that there are now 100 different strains circulating around the world and ransomware and cybercrime damages expected to hit $6 trillion this year. In research conducted by cybersecurity vendor Blackfog for its 2021 State of Ransomware report, the United States overwhelmingly leads the world in (known) ransomware attacks.
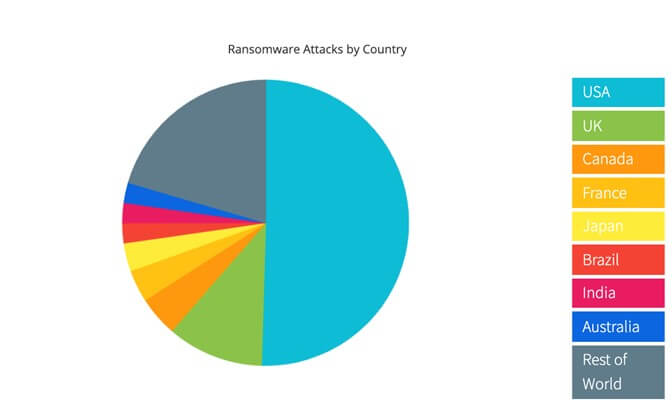
Image Credit: Blackfog
Also worth noting, and perhaps insight on why the U.S. government is interested in keeping closer tabs on ransom payments, is that government entities are at the top of the list for targets for ransomware threat actors, along with education, services industry, healthcare, tech, and manufacturing sectors. That’s no small pool of potential victims and these days, ransomware is big business and highly lucrative.
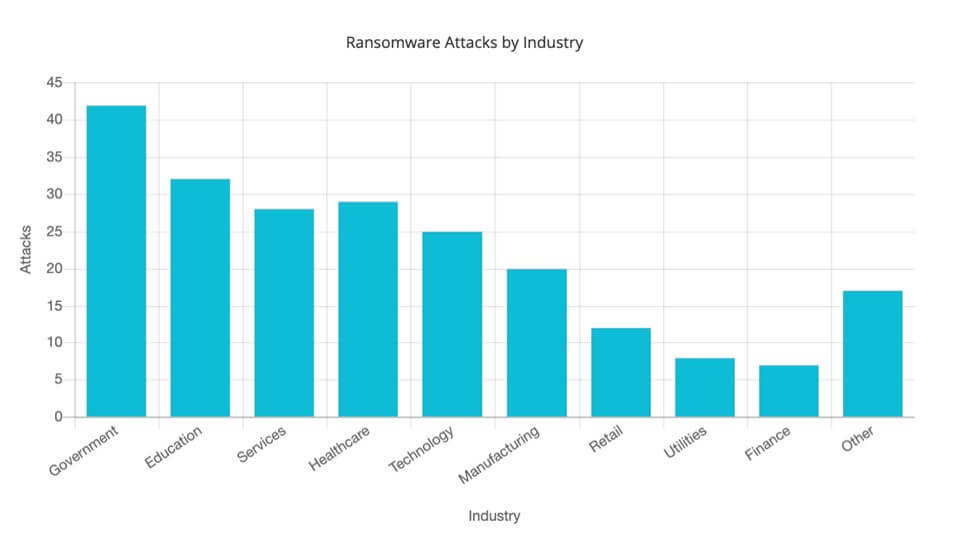
Image Credit: Blackfog
From a hard-numbers perspective, and based on data from Sonicwall in their Mid-Year Update: Sonicwall Cyber Threat Report, the ransomware scourge hit a staggering 304.7 million attempted ransomware attacks within SonicWall Capture Labs’ Capture Threat Network, which monitors and collects information from global devices. To put that in perspective, the firm logged 304.7 million ransomware attempts, 51.1 million cryptojacking attacks, 32.2 million IoT malware attacks, 2.5 billion malware attacks, 2.1 million encrypted threats, and 2.5 trillion intrusion attempts.
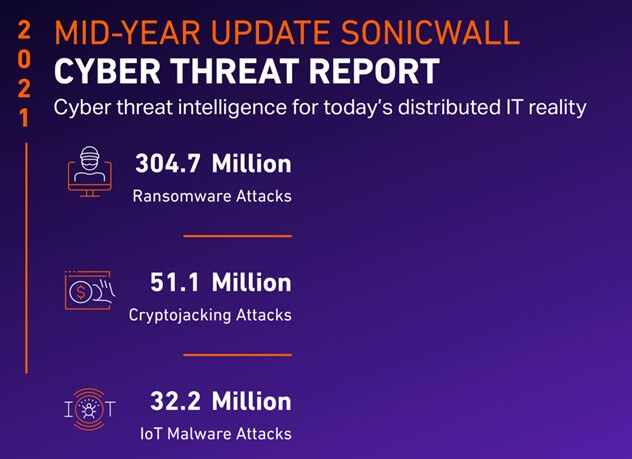
Image credit: Sonicwall
Ransomware is an Easy Path for Threat Actors
Colonial Pipeline, the JBS meat processor hack, attacks on hospitals and entire healthcare systems, ransomware attacks on government entities targeting governments of all sizes — cybercriminals are embracing ransomware because it’s a quick and easy way to make a lot of money without a lot of work. And now with ransomware-as-a-service offerings made available by ransomware gangs further looking to monetize opportunities, there’s no chance that ransomware threats are going to diminish.
That’s why The Ransom Act seems to be the right bill at the right time — or at least one of them — as the government takes steps to better understand ransomware threats and develops strategies to hunt cybercriminals and also mitigate the frequency of attacks along the way.
Futurum’s Cybersecurity Shorts Series Coverage of the Ransom Act
My colleague and fellow analyst Fred McClimans and I discussed The Ransom Act as part of our Futurum Tech Webcast Cybersecurity Shorts series. You can watch that conversation here:
Or stream the full episode, where we cover the goings on in the world of cybersecurity on a weekly basis on your favorite streaming channel here:
Don’t Miss An Episode – Subscribe Below:
Disclaimer: The Futurum Tech Webcast is for information and entertainment purposes only. Over the course of this webcast, we may talk about companies that are publicly traded and we may even reference that fact and their equity share price, but please do not take anything that we say as a recommendation about what you should do with your investment dollars. We are not investment advisors and we do not ask that you treat us as such.
Transcript:
Shelly Kramer: Well, speaking of ransomware attacks, that we’re going to wrap our show with a quick mention of the Warren bill, which is a Ransom Disclosure Act that’s been proposed by Senator Elizabeth Warren and Democratic representative, Deborah Ross. And this bill proposes that victims of ransomware attacks must report payments made to their hackers within 48 hours. And this would give, this Ransomware Disclosure Act would give the Department of Homeland Security data on ransomware payments, including the amount of money demanded, how much was paid, the kind of currency used, to your point. Bitcoin is actually traceable. And, this is really a couple of things. One, I’m sure it has to do with being able to recover, to find hackers, and recover ransomware that’s paid. But also, part of what these lawmakers said when they presented this bill is that it’s essential to bolster the government’s understanding of how hackers operate, and the extent of the ransomware threat.
And, our colleague, Ron Westfall, and I recorded a webcast yesterday and our 5G Factor Webcast. And one of the things we talked about there, happened to also be related to ransomware, and something that Nokia is doing from a Silicon level to protect against ransomware or to protect against cyber threats. And just, why this matters so much is really a pretty simple answer. So we’ve seen ransomware, the global attack volume of ransomware attacks has increased by 151% for the first six months of 2021, compared with this time of year, a year ago.
And, the FBI has warned that there are a hundred different strains of ransomware circulating around the world. And from a hard numbers perspective, that SonicWall Capture Labs reported that ransomware hit 304.7 million. There were 304.7 million attempted attacks. And, to put that in perspective, there were 304.6 million ransomware attacks for all of 2020. So this is part, the first six months of 2021, we’re already almost exactly the same in terms of the number of attacks that happened in a full year.
So, threat actors, we’ve had Colonial Pipeline, we’ve had JBS that shows the threat to our supply chains. Colonial Pipeline, critical infrastructure. We have had hacks of government systems. We’ve had hacks of hospital systems. I mean, the list is seemingly endless, but anyway, so this is, I thought that this was interesting to see, and I understand the logic here. There is other pending legislation around these things. I think, reporting breaches is one of the things that’s on the table and lots of different things, but this is a little bit different than some of the other things that’s been proposed, simply because it’s saying, “If you pay ransom, you are required to report it, so that we can do the work that we need to do from a Homeland Security standpoint.” So I thought that that was, it’ll be interesting to see, right? It’s a proposal, it’s not a law.
Fred McClimans: Yeah. And, this and other initiatives, TSA just announced this week that they’re going to mandate disclosures on the cyber-attacks from the railway and some of the other transportation providers. We need this information. The only way we learn what’s taking place, and have an opportunity to successfully track down, and apprehend, and recover is through a disclosure of this type of information. So I’m all for it.
Shelly Kramer: I am all for it as well.
The original version of this article was first published on Futurum Research.
Shelly Kramer is a Principal Analyst and Founding Partner at Futurum Research. A serial entrepreneur with a technology centric focus, she has worked alongside some of the world’s largest brands to embrace disruption and spur innovation, understand and address the realities of the connected customer, and help navigate the process of digital transformation. She brings 20 years' experience as a brand strategist to her work at Futurum, and has deep experience helping global companies with marketing challenges, GTM strategies, messaging development, and driving strategy and digital transformation for B2B brands across multiple verticals. Shelly's coverage areas include Collaboration/CX/SaaS, platforms, ESG, and Cybersecurity, as well as topics and trends related to the Future of Work, the transformation of the workplace and how people and technology are driving that transformation. A transplanted New Yorker, she has learned to love life in the Midwest, and has firsthand experience that some of the most innovative minds and most successful companies in the world also happen to live in “flyover country.”







